The first indicator was not a blaring alarm or a red flashing screen, but a microscopic discrepancy in the inbound packet sequencing.
I was sitting in the climate-controlled server room on the 42nd floor of the Chicago high-rise, a space that smelled faintly of ozone and dustless air. The ambient temperature was locked at exactly 68°. I liked the cold. It kept my mind sharp, or at least numb enough to tolerate the sheer, crushing boredom of corporate network auditing.
I leaned back in my ergonomic chair, watching the terminal lines scroll in pale green against the black monitor. My job was supposed to be invisible. I was an independent security contractor brought in to fortify the internal architecture before the quarterly board review. Most days I ran automated scripts, drank terrible breakroom coffee, and ignored the political warfare happening in the executive suite above me.
But my eyes caught a stutter in the data stream. A microsecond lag. The proxy server on the 39th floor was mirroring outbound traffic to an unauthorized external IP. Someone was siphoning the executive unencrypted drives.
I did not panic. Panic was for people who did not understand the machinery. I felt a slow, heavy waking in my chest, a lethargic engine turning over for the 1st time in months. The apathy that usually blanketed my brain began to lift, replaced by cold, mechanical focus.
I isolated the node.
The unauthorized access was tunneling directly through the credentials of Giovani Meyers, the senior director of operations. But the target was not general financial data. The target was the localized drive of the executive vice president, Stella Ryan.
I hit a keystroke to temporarily bottleneck the outbound port, slowing the leak without alerting the intruder that I was watching. Then I stood up. The problem required physical intervention. I had to pull the hard line from her office to sever the connection cleanly without triggering an automated wipe protocol.
I checked my watch. 6:45 in the evening. Most of the floor was empty, save for the cleaning crews and the executives who did not know how to go home.
I walked to the elevator, the heavy rubber soles of my boots making no sound on the polished concrete. The ride to the top floor was a silent vertical ascent into the rarified air of mahogany and glass.
I stepped out into the executive suite.
The lights were dimmed, casting long shadows across the thick carpeting. I navigated the maze of empty assistant desks until I reached the corner office at the end of the hall. The door was open.
I stopped in the doorway.
Stella Ryan was sitting behind her massive oak desk, the Chicago skyline, a grid of amber and silver lights, behind her. She leaned back in her high-backed leather executive chair, 1 knee crossed over the other. She wore a crisp white blouse with the collar open at the throat and a sharp black pencil skirt.
I stood there in my faded gray t-shirt, my hands resting in my pockets, the fabric of my jeans carrying the faint dust of the server racks. I was an anomaly in her polished world, a wrench dropped into a glass vase.
She looked up from the glowing screen of her laptop. The ambient light caught the exhaustion at the corners of her eyes, a tightness in her jaw that she hid beneath a perfectly calibrated professional mask. But when she saw me, the mask shifted. A tired, genuine amusement softened her features.
“William,” she said, her voice a low, melodic contrast to the sterile hum of the building. “To what do I owe the pleasure of a visit from the basement ghost?”
I did not step fully into the room yet. I maintained the distance, analyzing the situation. The data leak was active. Every second I stood there, more files were compiling in Giovani’s shadow folder. But I could not just tell her to step away from the machine. If she closed a window or triggered a save state, the malware might execute a deletion protocol. I needed to control the environment first.
“I need access to your terminal,” I said, my voice flat, devoid of urgency.
She arched an eyebrow, tapping a silver pen against her desk pad. “Right now I’m finalizing the quarterly projections for tomorrow’s board meeting, the 1 where Giovani is undoubtedly going to try and argue that my department is bleeding capital.”
“Right now,” I repeated. “And you need to stop typing.”
She sighed, a quiet sound of supreme fatigue, and let the pen drop. She looked at me, really looked at me, her gaze tracing the plain gray cotton of my shirt, the relaxed, immovable set of my shoulders. The tension in the room was not just digital. It was the quiet friction of 2 people who operated on completely different frequencies. She was motion, ambition, and perpetual stress. I was stillness, logic, and calculated restraint.
I pulled my left hand from my pocket and checked my watch again. 6:50.
“I have a hard out at 7,” I said, a strategic lie to see how she would react, to gauge her compliance under pressure. “I have a date.”
It was not a date. It was a scheduled calibration of a secondary server cluster on the west side. But the word hung in the air oddly heavy.
Stella stopped leaning back. She shifted her weight, uncrossing her legs, and planted her elbows on the desk, resting her chin on her steepled fingers. A slow, almost challenging smile curved her lips. She looked up at me, the angle of her gaze sharp and assessing.
“I told my boss I have a date,” she murmured, echoing my phrasing, testing the weight of it.
She tilted her head and said, “Is she prettier than I am?”
The silence in the office was immediate and absolute. The hum of the city outside seemed to fade.
I felt a sudden, distinct tightening at the base of my skull. It was not a spark or a flash. It was the heavy, undeniable gravity of an anchor dropping.
I did not smile back. I did not offer a compliment or a witty deflection. I simply held her gaze, my expression completely neutral, while my mind processed the sheer weight of her exhaustion hiding behind that playful deflection. Her knee bounced once under the desk, then stopped when she noticed. The click of her nails on the armrest kept a tight, uneven rhythm. When Giovani’s name came up, her smile held, but her breathing went shallow. So she kept the banter moving fast and bright just to keep the room from going quiet.
“She doesn’t exist,” I said plainly, my voice quiet. “Step away from the desk, Stella.”
The use of her first name, stripped of any corporate title, broke the spell. Her smile faltered, replaced by a sudden sharp clarity. She recognized the tone. It was the tone of someone who knew exactly what was wrong and was already implementing the fix.
She stood up, smoothing her skirt once, and stepped to the side.
I moved into the space she vacated. The leather of the chair still held the heat of recent use, and I ignored it. I did not sit. I leaned over the desk, my hands hovering over the keyboard. I did not touch the mouse. I used a series of command-line shortcuts, bringing up the hidden directory trees.
“What is it?” she asked, her voice dropping to a serious, hushed tone. She stood close to my shoulder, not close enough to touch, but close enough that I could sense the sudden stillness of her breathing.
“Someone is executing a localized packet capture on your machine,” I explained, my fingers moving in rapid staccato bursts across the keys. I was not trying to impress her. I was simply working at my baseline speed. “They are mirroring your personal directory to an external server. It’s a clumsy zero-day exploit piggybacking on the automated update service.”
“My personal directory.” Her voice tightened. “William, my drafts for the restructuring proposal are in there. My personal performance reviews of Giovani’s team.”
“I know.”
I kept my eyes on the screen.
“That’s why I’m killing the port.”
I input the final command string and hit enter. The screen flashed black for a fraction of a second, then returned to her spreadsheet. The outbound data flow dropped to 0. I exhaled a short, controlled breath. The immediate hemorrhage was stopped, but the wound was still open.
“Did they get it?” she asked.
I pulled up the system log, parsing the raw data. “They got fragments. Encrypted blocks. It will take them a few hours to compile it into anything readable.”
I stood up straight and turned to face her.
“But the protocol constraint is strict. Now that I’ve severed the connection manually, the localized network security policy automatically initiates a hard lockdown on this terminal. You can’t leave, and neither can I. We have to sit here and rebuild the encryption keys from scratch, or the automated system will purge your drive at midnight as a security measure.”
Stella stared at me. “You’re telling me we are locked out of the network unless we stay here and fix it. For how long?”
“Until it’s done.”
I looked at the digital clock on the wall.
“Cancel your plans. The date is off.”
She did not argue. She did not throw a tantrum. She just nodded, her shoulders dropping a fraction of an inch as she accepted the new reality. It was why I respected her. She did not waste energy fighting the immutable laws of physics or systems.
The next 3 hours were a masterclass in tedious, grinding precision. I commandeered her secondary monitor, turning the screen vertically to read the cascading lines of hexadecimal code. Stella sat on the small leather sofa in the corner of her office, her laptop open on her knees, working offline on her speech notes.
The silence between us was functional, a shared workspace where the only sounds were the rapid clacking of my mechanical keyboard and the soft rustle of her shifting papers.
Around 9:30, the tension in the room began to shift. The adrenaline of the initial breach had worn off, leaving behind the hollow ache of fatigue. I rubbed the back of my neck, feeling the knots of tension pulling at my spine. I had not eaten since noon.
“You stopped typing,” Stella noted from the sofa. She did not look up from her screen.
“Running a decryption algorithm,” I replied, leaning back in the chair. “It takes 12 minutes to brute force the hash. We wait.”
She finally closed her laptop and set it on the glass coffee table. She stood up, stretching her arms above her head. The movement was unselfconscious, betraying her exhaustion.
“I’m ordering food. Thai or Greek?”
“I don’t care. Whatever is fast.”
She ordered Thai.
While we waited, the dynamic in the room settled into a strange domestic quiet. I pulled my phone from my pocket to check a message from Christopher, my sole confidant and the man who had brokered my contract there. He was asking whether the network was stable.
I typed a single-word reply.
Handled.
Then I deliberately placed the phone face down on the corner of the desk. I pushed it a few inches away. It was a physical boundary. I was there. I was nowhere else.
Stella watched the movement. She walked over to the desk and leaned against the edge, crossing her arms.
“You don’t talk much, do you, William?”
“I communicate when data needs to be transferred,” I said, my tone dry, but lacking its usual biting edge.
She offered a small, tired smile.
“And what does the data say about who did this?”
I assessed whether she would understand the response better with the use of diagrams and decided a visual was the only way to explain the architecture of the betrayal.
I turned the monitor toward her.
“Look at this. This is the perimeter.” I pointed to the outer boundary on the schematic. “The red vectors are the intrusion paths. Notice how they bypass the external firewall completely. The attack didn’t come from outside. It was launched from within the intranet, specifically from a node authorized under Giovani Meyers’s credentials.”
Stella looked at the diagram, her eyes tracing the lines. The reality of the betrayal settled over her.
“He’s trying to find the restructuring drafts. He knows I’m recommending his department be cut by 30%.”
“He found the drafts,” I corrected gently, “but they are locked in an encrypted packet. I have the key. He doesn’t.”
Stella held my gaze. The panic that had been hovering at the edges of her vision began to recede, replaced by a profound, sudden stillness. The transfer of stability was palpable. I watched the tremor in her hands stop. She picked up her fork again.
“Okay,” she breathed.
Just 1 word, but it carried the weight of a surrendered burden.
By midnight, the fatigue was a physical weight in the room. I was back at the terminal, my eyes burning as I manually rebuilt the registry keys. Stella was asleep on the leather sofa. She had curled onto her side, her suit jacket draped over her shoulders like a blanket.
I paused my typing for exactly 5 seconds to look at her.
In the dim light of the monitors, stripped of her corporate armor, she looked remarkably fragile, yet completely resilient. I felt a sudden sharp ache in my chest, a pulling sensation, a quiet gravity that urged me to walk over and adjust the jacket to cover her arms.
I kept my hands on the keyboard.
I forced my focus back to the code.
Restraint was not a punishment. It was a discipline. The best way to protect her was not to hover over her while she slept. It was to ensure that when she woke up, her enemies had no weapons left to use against her.
At 2:00 a.m., the final progress bar hit 100%. The system locked the new encryption keys, sealing the drive in an impenetrable digital vault. The data leak was not only contained, but the stolen packets on Giovani’s server were rendered permanently inert.
I ran a secondary script to wipe the logs on his end, leaving him with corrupted, useless files.
I closed the terminal. The soft click of the mouse seemed loud in the quiet room.
Before I woke her, I built the paper trail.
First, the firewall logs went to an offline drive. Then each file got a SHA256 hash timestamped to the second. The intrusion path, the credential misuse, and the corrupted packet captures came next, printed, aligned, stapled, and signed on the top page. Down the hall, the night security supervisor witnessed the timestamps before the whole bundle was sealed in a plain envelope.
No speeches.
Just evidence that would survive a boardroom.
A single-line notice went to the CEO’s assistant. Security incident contained. Formal briefing at 8:30. Evidence on hand.
Stella stirred. She sat up slowly, rubbing her face, her hair falling out of its perfect arrangement. She looked at me, blinking against the light.
“Is it done?”
“It’s done,” I confirmed.
I stood up, stretching my back, the joints popping in the silence.
“Your drive is secure. The network is stabilized. The automated lockdown will lift at 6:00 a.m.”
She looked at the clock, then back at me.
“You stayed awake the entire time.”
“That was the job.”
“No,” she said, her voice gaining strength, the executive authority returning, but tempered with something much softer. “The job was to log the error and report it to IT tomorrow. You bypassed protocol to fix it yourself. You stayed.”
I did not have a logical defense for that.
So I said nothing.
I just gathered my jacket from the back of the chair.
“Get some sleep, Stella. You have a board meeting in 6 hours.”
The next morning, the atmosphere in the executive boardroom was charged with a toxic, electric anticipation.
I sat in the back row, a silent observer in my usual gray shirt, a stark contrast to the sea of bespoke navy and charcoal suits. I was required to be there as the security contractor to give the quarterly network health report, but my real purpose was to watch the architecture of Giovani’s plan collapse.
Stella stood at the head of the long mahogany table. She looked flawless. The exhaustion of the night before was completely erased, replaced by a radiant, terrifying competence. She began her presentation, outlining the financial projections with surgical precision.
Giovani Meyers sat halfway down the table. He was a man who wore his ambition like cheap cologne, overpowering and ultimately offensive.
He waited for his moment.
When Stella brought up the proposed budget cuts, he struck.
“If I may, Stella.”
Giovani interrupted, his voice dripping with false concern. He opened a manila folder in front of him.
“I think the board should be aware that your judgment regarding these cuts might be compromised. I received an anonymous data dump last night. It appears to be your personal files, drafts indicating a clear targeted bias against my department along with some highly unprofessional remarks regarding the CEO’s leadership.”
A low murmur rippled through the board members. The CEO, sitting at the far end, frowned deeply.
Stella did not flinch.
She did not look at me. She simply closed her presentation clicker and placed it on the table.
“An anonymous data dump, Giovani. That is a very serious allegation.”
“I have the files right here,” he said, pulling a flash drive from his pocket and sliding it across the polished wood. “I suggest IT decrypt this immediately for the board’s review.”
The CEO nodded. “Proceed.”
I stood up from the back row.
The room fell silent as I walked to the table.
I picked up the flash drive. It felt light, insignificant. I plugged it into the presentation laptop at the front of the room and mirrored the screen to the main projector.
I opened the drive.
A list of files appeared.
Giovani leaned back, a smug smile settling on his face.
I clicked the 1st file.
The screen filled with a chaotic, meaningless string of alphanumeric characters.
Corrupted data.
I clicked the next.
More corrupted data.
I ran a quick diagnostic script, projecting the results on the wall.
“This drive contains nothing but shattered hash fragments,” I stated, my voice carrying cleanly through the silent room. “The data is unreadable. Corrupted at the source.”
I paused, then delivered the final blow with methodical precision.
“Furthermore, the metadata on these fragments indicates they were illicitly scraped from an internal node using an unauthorized packet sniffer, a node registered to Giovani Meyers.”
The silence in the room shifted from tense to lethal.
Giovani’s smug smile vanished, replaced by pale, stammering panic.
“That’s impossible. The script was flawless. Someone tampered with it.”
“Yes,” Stella said, her voice cutting through the air like a blade. “Someone did.”
She reached into her own portfolio and pulled out a stack of paper.
“And just to ensure complete transparency with the board, I brought hard copies of my actual restructuring proposal. The 1 based on metrics, not bias.”
She tossed the stack onto the table.
Giovani looked around the room, finding no allies, only the cold, unforgiving stares of the board.
The CEO pointed a finger toward the door.
“My office, Giovani. Now.”
As Giovani gathered his things, utterly defeated, Stella stood tall. She did not gloat. She simply reclaimed her space.
She looked to the back of the room, her eyes meeting mine. The professional mask was in place for the board, but in the microexpressions, the slight softening of her mouth, the steady calm in her gaze, she was speaking directly to me.
We did it.
I nodded once, a barely perceptible dip of my chin, and walked out the back door before the congratulations began.
My job was done.
The aftermath was swift.
Giovani was terminated by noon. The board approved Stella’s restructuring plan and officially confirmed her promotion to senior EVP. The corporate machine ground on, absorbing the drama and turning it into policy.
At 6:00 p.m., I was packing my gear in the server room. The contract was complete. My temporary access badge was set to expire in 1 hour. I zipped my heavy canvas duffel bag, the sound loud in the quiet room.
“Are you leaving?”
I turned.
Stella was standing in the doorway of the server room. She had traded the heels for sensible flats, and the rigid posture of the executive was gone. She looked relaxed. Grounded.
“Contract is finished,” I said, hefting the bag over my shoulder. “Network is secure.”
She walked into the room. It was the 1st time she had been down there in my domain. She looked at the rows of blinking servers, the tangled cables, the cold utilitarian floor.
“You didn’t stay for the celebration lunch.”
“Not my scene.”
She stopped a few feet away from me.
“I need you to fix 1 more thing, William.”
I set the bag down. “What’s broken?”
She reached into her pocket and pulled out a small, heavy object. She held it out to me.
It was a brushed-steel guest access card, signed out from security and time-limited for 24 hours.
“My calendar,” she said, her voice quiet, steady, and completely stripped of corporate artifice. “It’s completely disorganized. I have a dinner reservation at 8 tonight and no 1 to go with.”
I looked at the card in her hand.
It was not just an invitation to dinner.
It was a clear, public choice.
I felt my jaw tighten once, then settle. I did not take the card immediately. I looked at her, searching her face for any sign of hesitation, any lingering fear.
There was none.
She was choosing this.
I reached out and took the card. My fingers brushed hers, the briefest point of contact, but it was enough to transfer the stability back and forth.
“I can fix a calendar,” I said, my voice dropping to that low, quiet tone I only used when the world was shut out.
She stepped closer until I could hear her breathing steady out. Her fingers caught the hem of my sleeve, not tugging, just holding me in place.
“William,” she said, soft but unambiguous.
She nodded once.
I did not pull her into a frantic embrace. I did not let adrenaline dictate the moment. I placed 1 hand at her waist, steady and respectful, and leaned down.
The kiss was not an exploration.
It was an arrival.
It was the heavy, absolute finality of a lock sliding into place, sealing a door against the storm outside. There was no desperation, no messy urgency. It was a promise signed without ink, a mutual acknowledgment that the wandering had stopped.
I felt the tension bleed out of her shoulders under my hand, her exhale steadying as we parted.
“8:00,” she whispered, a soft smile returning to her lips.
“I’ll be there,” I replied.
I picked up my bag, and the weight of it felt different now, lighter. I watched her walk back to the elevator, her steps steadier, her posture relaxed.
The server room felt a little too quiet after she left, but it did not feel empty anymore.
The guest card stayed in my pocket, not as a promise, just as a plan.
The truest anchor when a system crashes is the person who chooses to stay and do the work. A green flag is simple. Calm under pressure, clear boundaries, and receipts that stand up in daylight.
News
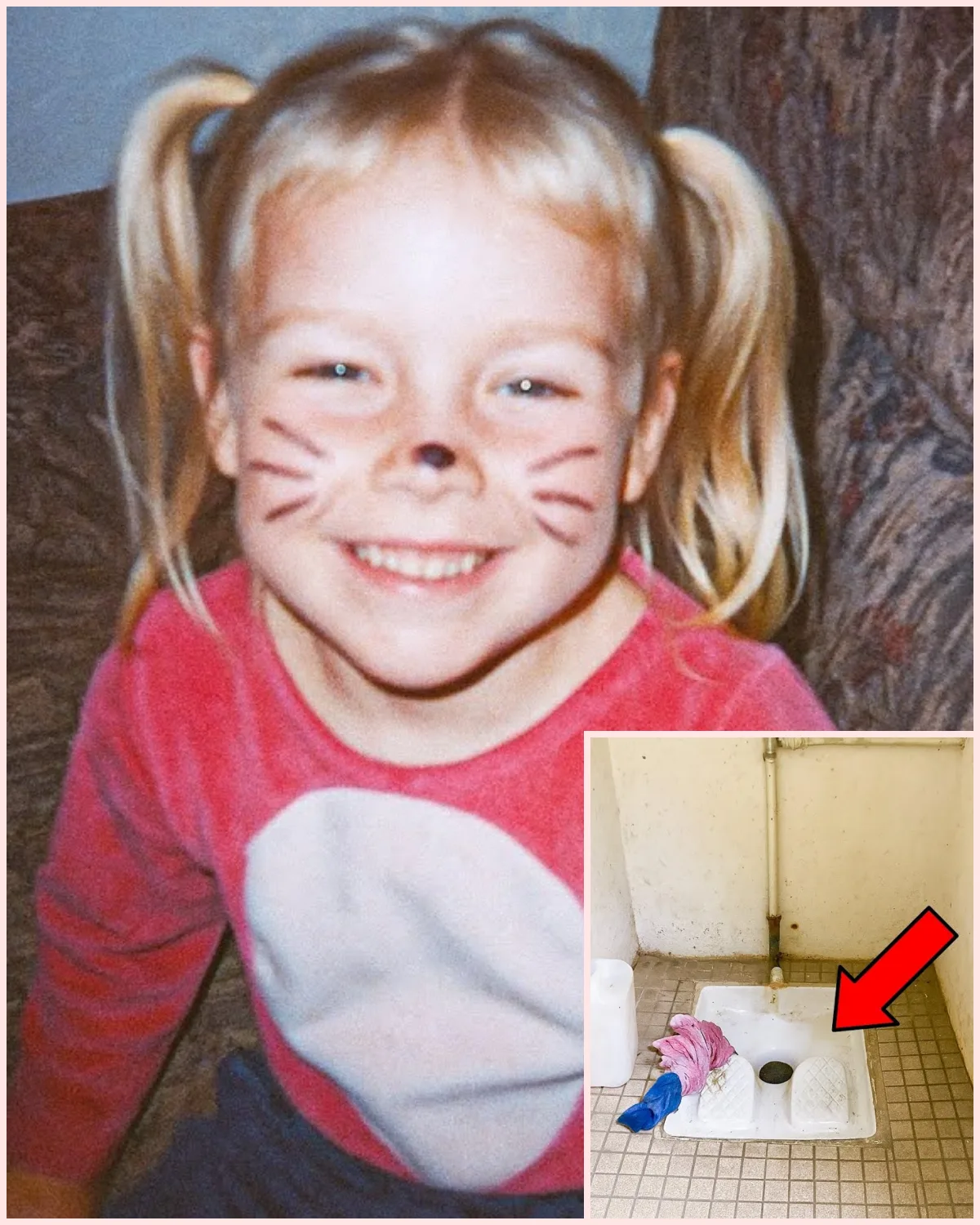
Girl Vanished From Driveway, 2 Years Later a Public Restroom Gives a Disturbing Clue…
Girl Vanished From Driveway, 2 Years Later a Public Restroom Gives a Disturbing Clue… The pink sweatshirt should have been in a donation box or tucked away in a memory chest, anywhere but where it was found. Amanda Hart was 4 years old when she vanished from her own driveway on a sunny afternoon […]
Single Dad Driver Kissed Billionaire Heiress to Save Her Life—What Happened Next Changed Everything
Single Dad Driver Kissed Billionaire Heiress to Save Her Life—What Happened Next Changed Everything The ballroom glittered like a jewelry box, all crystal chandeliers and champagne towers. 200 guests in designer gowns stood beneath the lights, pretending they cared about charity. Nathan stood in the corner, scanning faces the way he had been trained […]
“They Sent Her as a Joke Because of Her Weight… The Mafia Boss’s Response Silenced the Room.
“They Sent Her as a Joke Because of Her Weight… The Mafia Boss’s Response Silenced the Room. The wedding of the year glittered beneath the chandeliers of the Beverly Hills Grand Hotel. Champagne flutes sparkled in manicured hands. Violins filled the marble hall with gentle music, and waiters in white gloves glided across the […]
“I Ran Into My Ex-Wife’s Mom by the Poolside… What Happened Next Changed Everything”
“I Ran Into My Ex-Wife’s Mom by the Poolside… What Happened Next Changed Everything” The divorce had been final for 6 weeks, but Tom Parker still woke each morning feeling as though it had happened only hours earlier. He would open his eyes in the silence of his apartment and remember, all over again, that […]
“I’m Still a Man, Claire” — Whispered the Paralyzed Billionaire to His Contract Bride
“I’m Still a Man, Claire” — Whispered the Paralyzed Billionaire to His Contract Bride Clare Donovan’s heels clicked against Italian marble as she stepped into the penthouse elevator at the Cromwell, Manhattan’s most exclusive residential tower. Her portfolio bag felt heavier than usual, weighed down by rejection letters and final-notice bills tucked inside. At 26, […]
My Boss Sat On My Lap At The Beach And Said: “Don’t Move, My Ex Is Watching.”
My Boss Sat On My Lap At The Beach And Said: “Don’t Move, My Ex Is Watching.” Ethan Campbell was 29 and worked as a marketing specialist at a large tech firm in Tampa, Florida. Most days, his life was quiet and steady. He got up early, drove to the office, sat through meetings, […]
End of content
No more pages to load