At 3:58 a.m., while most of Memphis slept under the weight of a humid summer night, a line of unmarked federal SUVs exited the I-240 bypass and disappeared into the industrial sprawl south of Memphis International Airport. There were no flashing lights, no sirens, no visible signs that anything unusual was unfolding. Only the steady rumble of engines, the faint glow of cargo cranes in the distance, and the low drone of aircraft taxiing for early-morning departures.
To a casual observer, the destination looked unremarkable: a cluster of aging warehouses scattered along cracked access roads, indistinguishable from hundreds of other forgotten buildings that dot the logistics belt surrounding the city. But to the federal agents moving quietly between loading docks and rusted freight doors, this place had already revealed itself as something far more dangerous. What lay inside Warehouse Complex 314, according to weeks of intelligence analysis, was not abandoned infrastructure, but the visible edge of a system designed to hide in plain sight.
By dawn, 44 missing children would be removed from that system. The evidence uncovered would suggest that the operation in Memphis was neither spontaneous nor isolated, but part of a broader, highly organized network that had functioned for years by embedding itself within America’s freight and logistics corridors.
Patterns in the Noise
The investigation did not begin with a tip or a dramatic confession. It began with data—quiet anomalies that only became meaningful when layered together.
Shipping manifests appeared with missing pages. Nighttime freight deliveries were logged without corresponding drivers or vehicle registrations. Electrical usage spiked at a property officially listed as vacant, drawing more power between midnight and 4 a.m. than nearby medical facilities. Separately, missing children reports filed across western Tennessee and northern Mississippi began to show an unsettling alignment with cargo truck departure times.
On their own, none of these indicators were definitive. Together, they formed a pattern that analysts could not ignore.
Warehouse Complex 314, a 70-year-old distribution center south of the airport, became the focal point. Official records described it as empty. Utility data suggested otherwise. Surveillance flights detected persistent thermal signatures at night, consistent with human presence. The building, it seemed, was dormant only on paper.
By the time the convoy arrived shortly before 4 a.m., investigators already believed that the site functioned as an intake and transfer point for children being moved through the Memphis freight grid. What they did not yet know was how extensive, or how disciplined, the operation inside would prove to be.
The First Breach
The initial breach came without warning. A battering ram struck a welded emergency exit, sending vibrations through the steel frame. The door buckled inward and tore free with a sound that echoed through the empty lot. A rush of warm, stale air poured out, carrying the sharp scent of chemical disinfectant mixed with sweat and something sour that several agents would later describe as unforgettable.
Flashlights cut through the darkness. What they revealed immediately challenged any assumption of disorder or improvisation.
The corridor beyond the door was lined with plastic sheeting. Scuff marks covered the floor and walls—small footprints, repeated patterns, evidence of frequent movement. Blue tape strips ran along the concrete, each numbered in sequence, guiding traffic deeper into the building.
At the end of the hall, agents entered a space that was clearly not meant for storage. Rows of folding chairs were bolted to the floor, each marked with a colored tag. Water bottles and half-eaten meal bars were scattered beneath them. A whiteboard mounted on the wall listed times under headings such as “Arrival,” “Processing,” and “Transfer,” with numbers written in red marker.
The operation had not been abandoned. It had simply paused.
Behind a makeshift tarp wall, agents found the first children—five of them, huddled together on bare concrete. Their hair had been cut unevenly. Their clothing did not match. Shoelaces were missing. One boy, perhaps nine years old, stared ahead with shallow, mechanical breathing. A younger girl clutched a plastic container of crayons, all of them chewed flat at the ends.
She flinched when a flashlight beam passed over her face.
A System, Not a Scene
As teams pushed farther inside Warehouse 314, the layout shifted. Pallets had been arranged into corridors. LED strips powered by car batteries illuminated narrow paths leading to clearly defined sections: intake, medical holding, sorting.
In one area, agents found a folding table covered with latex gloves, cotton pads, and syringes filled with diluted sedatives. Nearby were rubber wristbands stamped with state abbreviations: MS, AL, AR. The implication was immediate and disturbing. This was not a local operation. Children were being moved across state lines.
At the eastern loading bay, another team discovered three cargo trailers backed directly into the building. Inside, plywood compartments lined with insulation foam created cramped enclosures. Some were empty. Others contained blankets still shaped by recent use. On the floor of one trailer lay a small pink sneaker, warm to the touch.
Someone had been taken from that space minutes earlier.
Overhead, footsteps echoed on a steel catwalk. The traffickers, it seemed, were still inside.
The Mezzanine Office
The chase up the catwalk led to a mezzanine overlooking the warehouse floor. Here, the operation’s administrative core came into view.
Computers sat open, logged in, spreadsheets still active. A corkboard covered an entire wall, layered with printed maps of Tennessee, Mississippi, and Arkansas. Red circles marked transport corridors. Blue arrows pointed toward rail junctions. Green triangles indicated “safe sites.”
Pinned at the center was a photograph of Warehouse 314 itself, taken months earlier.
The site had not been chosen at random. It had been studied, tested, fortified.
One suspect escaped through a window using a rope improvised from knotted bed sheets. Others did not. But even as arrests were made and children were escorted out, analysts reviewing the digital material understood that what they were seeing represented only a fraction of the whole.
At 5:12 a.m., inside a mobile command truck parked outside the complex, encrypted folders pulled from the mezzanine computers began to open.
What initially looked like disorganized scheduling data resolved into something precise and synchronized. Time stamps aligned with highway intersections. Codes corresponded to specific routes. Two additional locations appeared repeatedly, both active within the last six hours.
Neither had been previously associated with trafficking investigations.
Orange Mound and the Basement Church
One of the sites was an aging brick church in the Orange Mound neighborhood. The structure had once been a community anchor. Now it sagged under peeling paint and boarded windows.
Approaching from an overgrown alley, agents detected multiple small heat signatures beneath the building. Too many to be a single family. Too still to be a gathering.
When the reinforced basement door was breached, warm, stagnant air poured out, heavy with dust and ammonia. Inside, the basement had been stripped and transformed into a processing tunnel. Blankets were folded in identical stacks. Shoes were lined heel to heel along the walls. Food and water were arranged with regimented precision.
Twelve children sat on gym mats, knees pulled to their chests. Some blinked slowly in the light. Others stared at the floor. One boy repeated a phrase under his breath, over and over.
“Stay small. Stay quiet. Stay still.”
On a chalkboard, routes were mapped along major Memphis arteries. Above them, written in block letters, was a single instruction: Night only.
The Riverfront Dispatch Office
The second site—a trucking dispatch office near the riverfront freight yard—appeared operational from the outside. Inside, the illusion of normality was carefully maintained. Clipboards hung neatly. Coffee cups sat half full. Dispatch software ran continuously.
But the movements it displayed were fabricated. Trucks that did not exist. Routes that led nowhere.
Behind a door disguised as a janitor’s closet, agents found a staircase descending into a basement lined with makeshift holding cubicles. Wristbands marked with state abbreviations filled plastic bins. A child’s backpack lay open on the floor, still warm.
Here, investigators concluded, was a regional hub—routing children toward different interstate corridors depending on truck availability.
The handwriting on intake logs matched that found at Warehouse 314. Stickers on water bottles were identical. And the same triangular symbol—three intersecting lines—appeared again.
This was orchestration, not chaos.
The South Loop Revelation
One term appeared repeatedly in the data recovered from both sites: South Loop site – emergency only.
By 7 a.m., analysts understood its significance. This was not a fallback. It was the nerve center.
A reconnaissance drone soon confirmed activity in a derelict industrial strip south of the Airways Boulevard loop. Vans were parked tightly together. Figures moved between them. At least ten children were visible in the grainy feed.
When tactical units arrived, the stillness of the site was unsettling—not empty, but anticipatory. Fresh tire tracks cut through the mud. A generator hummed.
Inside the warehouse, children stood in taped squares on the floor, clutching small bags or nothing at all. Bandages were taped loosely to skin. Faces were gray with exhaustion.
This was not storage. It was a departure terminal.
Evidence of a Larger Design
As suspects attempted to flee and data technicians worked to recover destroyed hard drives, the scope of the operation became clearer. Files mapped freight routes across the southeastern United States. Recruitment zones spanned multiple states. Internal memos referenced inspection cycles, audit-sensitive corridors, and transport windows.
The language suggested insider knowledge of federal procedures.
Someone with authority had helped build this pipeline.
By 8 a.m., the sun rose over Memphis, casting long shadows across the exposed site. Medics treated children under tents. One boy asked repeatedly whether he would have to line up again. A paramedic told him no.
Inside the warehouse, investigators found a laminated checklist titled Before Departure. Items included water rations, sedation timing, and appearance checks.
Children had been reduced to inventory.
What Remains
By mid-morning, it was clear that the network had not been destroyed. It had fractured. Memphis, investigators now believed, was a command node within a much larger lattice—one that extended far beyond Tennessee.
As children were reunited with families and evidence was boxed for transport, the agents on scene shared a sober understanding. Dozens of lives had been saved that morning. But the machinery exposed in Memphis had been built over years, embedded within systems designed for commerce, not exploitation.
The challenge ahead would not be measured in raids or arrests alone, but in whether institutions could confront how easily such a system had hidden among them, unnoticed, for so long.
This was not the end of the investigation. It was the moment the scale of the problem finally came into focus.
Part Two: Following the Routes No One Was Meant to See
By the time the last child was led out from the South Loop warehouse, investigators already understood a hard truth: the arrests and rescues in Memphis marked an interruption, not a conclusion. What had been exposed overnight was not a single criminal ring but a logistics architecture—one that mirrored legitimate freight operations so closely it had survived for years inside the background noise of American commerce.
The question facing authorities that morning was no longer what happened here, but how far does it go.
A Network Built Like a Corporation
Inside the armored command truck parked near the South Loop site, analysts worked in shifts as evidence streamed in from three locations simultaneously. The recovered hard drive—damaged but readable—became the central artifact. What emerged from it was not a list of names or a conventional hierarchy, but something far more disciplined.
Folders were organized by corridor, not by person. Each corridor corresponded to a real-world freight artery: interstate highways, rail spurs, river-adjacent truck routes. Within those folders were schedules calibrated to law enforcement patrol cycles, holiday freight surges, and known inspection slowdowns. In several instances, routes were annotated with notes such as “low variance,” “inspection fatigue,” or “handoff blind.”
Investigators recognized the language immediately. It was the vocabulary of supply chain optimization.
The implication was stark. This network had been designed by someone who understood logistics not as theory, but as practice—someone familiar with how cargo actually moves across the southeastern United States, and where oversight predictably thins.
The Geography of Silence
As data teams expanded their analysis, a constellation of cities began to surface repeatedly. Financial transfers and shell-company registrations pointed toward regional freight hubs rather than major metropolitan centers. Among them were Little Rock, Shreveport, Jackson, and Birmingham.
None of these locations were unusual on their own. Each sat at the intersection of highways, rail lines, or river transport routes. Together, they formed a quiet lattice—a distribution map that allowed children to be moved incrementally, in small groups, without triggering attention.
One analyst described it later as “geographic laundering.” No single transfer looked exceptional. Only when viewed collectively did the system reveal its purpose.
The Insider Problem
The most troubling discovery came not from maps or schedules, but from internal memos buried deep within a directory labeled core admin – protected. The documents referenced inspection exemptions, early warnings about compliance audits, and timing notes that aligned too precisely with real-world enforcement actions to be coincidence.
These were not guesses. They were confirmations.
Several messages suggested advance knowledge of temporary inspection slowdowns at weigh stations and border checkpoints. Others referenced “federal cycle adjustments” and “window compression,” terms rarely used outside regulatory or enforcement environments.
Investigators were careful in their language, but the conclusion was unavoidable: someone with access to restricted operational knowledge had assisted in building or maintaining the network.
This was not necessarily a single individual, nor did it require direct participation in trafficking. Even limited leakage of procedural information—shared casually or deliberately—would have been enough to reinforce the system’s resilience.
Children as Units of Movement
As case agents reviewed intake logs recovered from the three Memphis sites, patterns emerged that deepened the sense of methodical cruelty. Children were not grouped by age or gender alone, but by what the logs referred to as “transfer tolerance.”
Younger children were scheduled for shorter hops. Older children were routed farther, sometimes crossing multiple states in a single night. Sedation levels were calculated accordingly. Compliance notes appeared beside several entries, reduced to symbols and shorthand marks.
One log included a column titled “visibility,” with notations indicating hair length, clothing condition, and likelihood of drawing attention during transit. The goal, investigators concluded, was not just concealment, but normalization—ensuring that no child looked out of place inside a truck stop, rest area, or loading bay.
Why Memphis Mattered
In the days following the operation, senior officials repeatedly returned to one question: why Memphis?
The answer lay in infrastructure. The city sits at the crossroads of major interstate highways, one of the busiest inland river ports in the country, and a dense rail network feeding the Southeast and Midwest. Cargo moves through Memphis at all hours, in volumes so large that anomalies disappear unless someone is actively searching for them.
Equally important was the city’s industrial geography. Aging warehouses, decommissioned freight buildings, and underutilized church and commercial spaces provided cover. Properties could remain officially vacant while quietly drawing power and traffic after midnight.
Memphis was not chosen because it was weak. It was chosen because it was efficient.
The Moment of Fracture
By late morning, law enforcement agencies across multiple states had been notified. Quiet alerts went out to freight inspectors, child protection units, and financial crimes divisions. No public announcement was made. Officials feared that premature disclosure would trigger rapid displacement of remaining network elements.
The lead analyst summarized the situation during an internal briefing with a sentence that would later circulate widely within investigative circles:
“This system doesn’t collapse when you remove a node. It adapts.”
The operation in Memphis had forced a fracture—routes compromised, schedules exposed, trust disrupted. But the underlying logic of the network remained intact, at least in part. Whoever had designed it had anticipated disruption and built contingency into every layer.
Lives Interrupted, Not Yet Reclaimed
Outside the command structure, the human consequences unfolded more slowly. Children were transported to medical facilities and child advocacy centers. Some were reunited with families within hours. Others could not yet say where they came from, or would not.
Trauma specialists noted a common pattern: many children struggled with open-ended questions. They were accustomed to instructions, not choices. When asked what they wanted, several responded with silence, or asked what they were supposed to say.
One clinician described the process ahead as “unlearning logistics”—helping children rediscover autonomy after being managed as freight.
An Investigation That Cannot Close
As evening approached on the day of the raids, evidence teams were still cataloging materials from the South Loop site. Spray-painted triangles appeared on beams and pallets throughout the building, a recurring symbol investigators now believed functioned as an internal verification mark—confirmation that a site or shipment was “cleared.”
The symbol had not yet been decoded. But its repetition suggested identity, continuity, and confidence.
For the agencies involved, the message of the Memphis operation was sobering. They had uncovered a machine that did not rely on secrecy alone, but on familiarity—on the assumption that no one would look too closely at systems that appeared ordinary.
Part Three will examine how such a network could operate for years without detection, and what structural vulnerabilities allowed it to hide in plain sight across state lines.
News
You are nothing but an illiterate servant. Do not speak to me until you learn to read proper English.”
You are nothing but an illiterate servant. Do not speak to me until you learn to read proper English.” The silence that followed was not merely a pause in conversation but a vacuum that seemed to draw the air from the most expensive dining room in Manhattan. Forks froze midair. A waiter 3 tables away […]
“This is today’s last batch, Mr. Huxley.”
“This is today’s last batch, Mr. Huxley.” Chloe Johnson stood beside her grandmother as a line of carefully selected women waited to be inspected like merchandise. Her grandmother’s eyes narrowed with practiced impatience, unimpressed by the parade. Chloe tried to keep the mood light, coaxing her to choose someone—anyone—so she could finally stop hearing complaints […]
I Need A Mother For My Sons And You Need Shelter —The Rich Cowboy Proposed To The Poor Teacher
The wind came howling across the Montana plains like the devil himself was chasing it, carrying snowflakes sharp as broken glass. Elellanor Hayes pulled her thin woolen shawl tighter around her shoulders and pressed her back against the rough bark of a cottonwood tree, but the cold bit through her worn dress just the same. […]
He was
They called me defective during toteminovida and by age 19, after three doctors examined my frail body and pronounced their verdict, I started to believe them. My name is Thomas Bowmont Callahan. I’m 19 years old and my body has always been a betrayal—a collection of failures written in bone and muscle that never properly […]
A Baby in 1896 Holds a Toy — But Look Closely at His Fingers
On a cool autumn afternoon, she found herself wandering through the narrow aisles of Riverside Antiques in Salem, Oregon. The sharp smelled of aged wood, old paper, and forgotten memories. Dust floated gently through thin beams of light that slipped in through the tall front windows. Shelves were crowded with porcelain dolls, tarnished silverware, faded […]
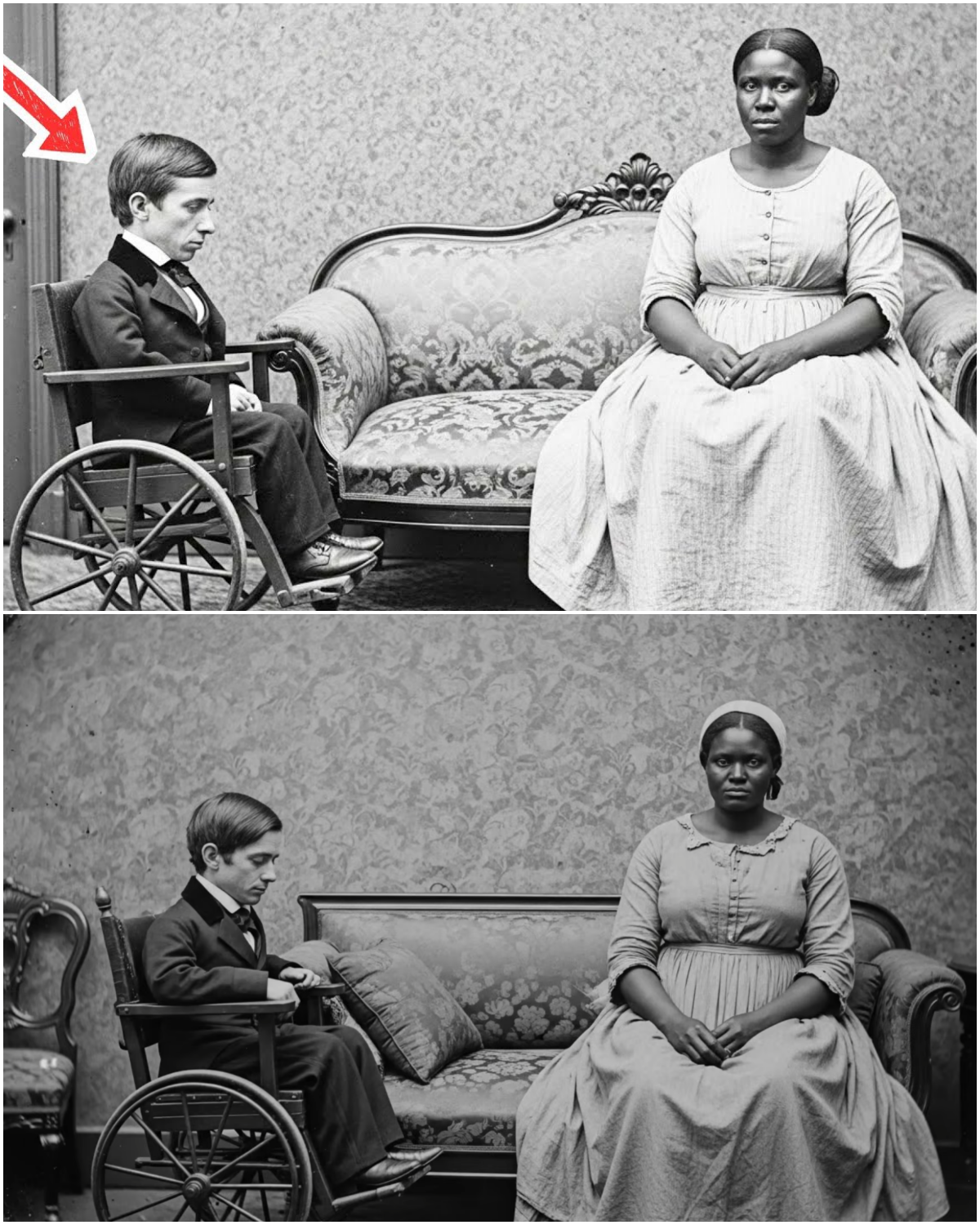
My stepmother forced me to marry a young, wealthy but disabled teacher
The rain did not fall in Monterrey; it hammered, a relentless rhythmic assault against the stained-glass windows of the Basilica del Roble. Inside, the air smelled of stale incense and the suffocating sweetness of a thousand white lilies, a scent Isabella Martínez would forever associate with the death of her freedom. She stood at the […]
End of content
No more pages to load